[ad_1]
A threat actor known as Prolific Puma has been maintaining a low profile and operating an underground link shortening service that’s offered to other threat actors for at least over the past four years.
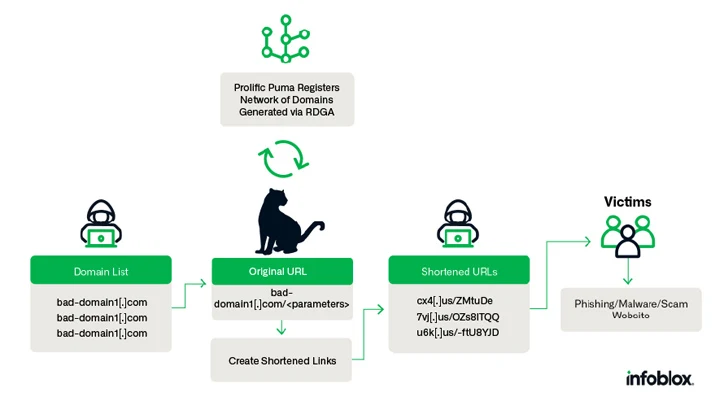
Prolific Puma creates “domain names with an RDGA [registered domain generation algorithm] and use these domains to provide a link shortening service to other malicious actors, helping them evade detection while they distribute phishing, scams, and malware,” Infoblox said in a new analysis pieced together from Domain Name System (DNS) analytics.
With malicious actors known to use link shorteners for phishing attacks, the adversary plays an important role in the cybercrime supply chain, registering between 35,000 to 75,000 unique domain names since April 2022. Prolific Puma is also a DNS threat actor for leveraging DNS infrastructure for nefarious purposes.
A notable aspect of the threat actor’s operations is the use of an American domain registrar and web hosting company named NameSilo for registration and name servers due to its affordability and an API that facilitates bulk registration.
Prolific Puma, which does not advertise its shortening service on underground markets, has also been observed resorting to strategic aging to park registered domains for several weeks prior to hosting their service with anonymous providers.
“Prolific Puma domains are alphanumeric, pseudo-random, with variable length, typically 3 or 4 characters long, but we have also observed SLD labels as long as 7 characters,” Infoblox explained.
Furthermore, the threat actor has registered thousands of domains in the U.S. top-level domain (usTLD) since May 2023, repeatedly using an email address containing a reference to the song OCT 33 by a psychedelic soul band called Black Pumas: blackpumaoct33@ukr[.]net.
The real-world identity and origins of Prolific Puma remains unknown as yet. That said, multiple threat actors are said to be using the offering to take visitors to phishing and scam sites, CAPTCHA challenges, and even other shortened links created by a different service.
In one instance of a phishing-cum-malware attack documented by Infoblox, victims clicking on a shortened link are taken to a landing page that requests them to provide personal details and make a payment, and ultimately infect their systems with browser plugin malware.
The disclosure comes weeks after the company exposed another persistent DNS threat actor codenamed Open Tangle that leverages a large infrastructure of lookalike domains of legitimate financial institutions to target consumers for phishing and smishing attacks.
“Prolific Puma demonstrates how the DNS can be abused to support criminal activity and remain undetected for years,” it said.
Kopeechka Hacking Tool Floods Online Platforms with Bogus Accounts
The development also follows a new report from Trend Micro, which found that lesser-skilled cybercriminals are using a new tool called Kopeechka (meaning “penny” in Russian) to automate the creation of hundreds of fake social media accounts in just a few seconds.
“The service has been active since the beginning of 2019 and provides easy account registering services for popular social media platforms, including Instagram, Telegram, Facebook, and X (formerly Twitter),” security researcher Cedric Pernet said.
Kopeechka provides two types of different email addresses to help with the mass-registration process: email addresses hosted in 39 domains owned by the threat actor and those that are hosted on more popular email hosting services such as Gmail, Hotmail, Outlook, Rambler, and Zoho Mail.
“Kopeechka does not actually provide access to the actual mailboxes,” Pernet explained. “When users request for mailboxes to create social media accounts, they only get the email address reference and the specific email that contains the confirmation code or URL.”
It’s suspected that these email addresses are either compromised or created by the Kopeechka actors themselves.
With online services incorporating phone number verification to complete registration, Kopeechka enables its customers to choose from 16 different online SMS services, most of which originate from Russia.
Besides accelerating cybercrime and equipping threat actors to launch full-fledged operations at scale, such tools – created as part of the “as-a-service” business model – highlight the professionalization of the criminal ecosystem.
“Kopeechka’s services can facilitate an easy and affordable way to mass-create accounts online, which could be helpful to cybercriminals,” Pernet said.
“While Kopeechka is mainly used for multiple accounts creation, it can also be used by cybercriminals who want to add a degree of anonymity to their activities, as they do not need to use any of their own email addresses to create accounts on social media platforms.”
[ad_2]
Source link