[ad_1]
The Iranian threat actor known as Agrius is leveraging a new ransomware strain called Moneybird in its attacks targeting Israeli organizations.
Agrius, also known as Pink Sandstorm (formerly Americium), has a track record of staging destructive data-wiping attacks aimed at Israel under the guise of ransomware infections.
Microsoft has attributed the threat actor to Iran’s Ministry of Intelligence and Security (MOIS), which also operates MuddyWater. It’s known to be active since at least December 2020.
In December 2022, the hacking crew was attributed to a set of attempted disruptive intrusions that were directed against diamond industries in South Africa, Israel, and Hong Kong.
These attacks involved the use of a .NET-based wiper-turned-ransomware called Apostle and its successor known as Fantasy. Unlike Apostle, Moneybird is programmed in C++.
“The use of a new ransomware, written in C++, is noteworthy, as it demonstrates the group’s expanding capabilities and ongoing effort in developing new tools,” Check Point researchers Marc Salinas Fernandez and Jiri Vinopal said.
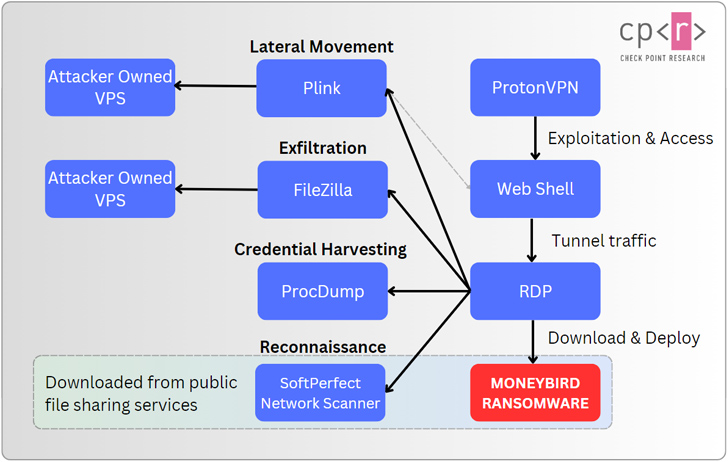
The infection sequence begins with the exploitation of vulnerabilities within internet-exposed web servers, leading to the deployment of a web shell referred to as ASPXSpy.
In the subsequent steps, the web shell is used as a conduit to deliver publicly-known tools in order to perform reconnaissance of the victim environment, move laterally, harvest credentials, and exfiltrate data.
Also executed on the compromised host is the Moneybird ransomware, which is engineered to encrypt sensitive files in the “F:User Shares” folder and drop a ransom note urging the company to contact them within 24 hours or risk getting their stolen information leaked.
“The use of a new ransomware demonstrates the actor’s additional efforts to enhance capabilities, as well as hardening attribution and detection efforts,” the researchers said. “Despite these new ‘covers,’ the group continues to follow its usual behavior and utilize similar tools and techniques as before.”
Zero Trust + Deception: Learn How to Outsmart Attackers!
Discover how Deception can detect advanced threats, stop lateral movement, and enhance your Zero Trust strategy. Join our insightful webinar!
Agrius is far from the only Iranian state-sponsored group to engage in cyber operations targeting Israel. A report from Microsoft last month uncovered MuddyWater’s collaboration with another cluster dubbed Storm-1084 (aka DEV-1084) to deploy the DarkBit ransomware.
The findings also come as ClearSky disclosed that no fewer than eight websites associated with shipping, logistics, and financial services companies in Israel were compromised as part of a watering hole attack orchestrated by the Iran-linked Tortoiseshell group.
In a related development, Proofpoint revealed that regional managed service providers (MSPs) within Israel have been targeted by MuddyWater as part of a phishing campaign designed to initiate supply chain attacks against their downstream customers.
The enterprise security firm further highlighted escalating threats to small and medium-sized businesses (SMBs) from sophisticated threat groups, which have been observed leveraging compromised SMB infrastructure for phishing campaigns and financial theft.
[ad_2]
Source link