[ad_1]
Cyberwarfare / Nation-State Attacks
,
Fraud Management & Cybercrime
,
Mobile Payments Fraud
APT41 Used WyrmSpy and DragonEgg Surveillance Malware to Target Android Users
Security researchers say a Chinese state-sponsored espionage group is using WyrmSpy and DragonEgg surveillance malware to target Android mobile devices.
See Also: OnDemand | Understanding Human Behavior: Tackling Retail’s ATO & Fraud Prevention Challenge
Researchers at cybersecurity company Lookout said APT41, also tracked as Barium, Earth Baku and Winnti, primarily relies on web application attacks and software vulnerabilities and uses WyrmSpy and DragonEgg to target organizations globally.
The company said APT41 recently switched tactics to develop malware specific to the Android operating system, relying on existing command-and-control infrastructure, IP addresses and domains to communicate with and issue commands to the two malware variants.
APT41 historically exploited specific web applications and software vulnerabilities to carry out surveillance on predefined target organizations. According to Mandiant, the group in May 2021 exploited a zero-day vulnerability in the USAHerds application and several vulnerable internet-facing web applications to successfully compromise at least six U.S. state government networks.
Research by Recorded Future’s Insikt Group also revealed that the cyberespionage group, along with the Tonto Team, had targeted four regional dispatch centers responsible for operating India’s power grid shortly after India and China had engaged in border clashes that resulted in combat-related casualties for the first time in 45 years.
Android Malware Historically Not on APT41’s Playbook
According to Lookout, APT41 likely used social engineering to distribute WyrmSpy and DragonEgg surveillance malware to Android devices, often by disguising the former as a default Android system application and the latter as third-party Android keyboards and messaging applications such as Telegram.
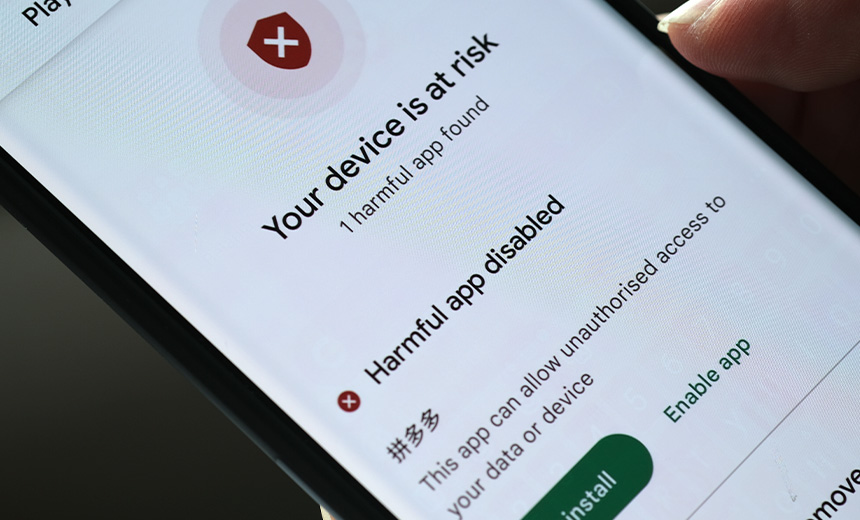
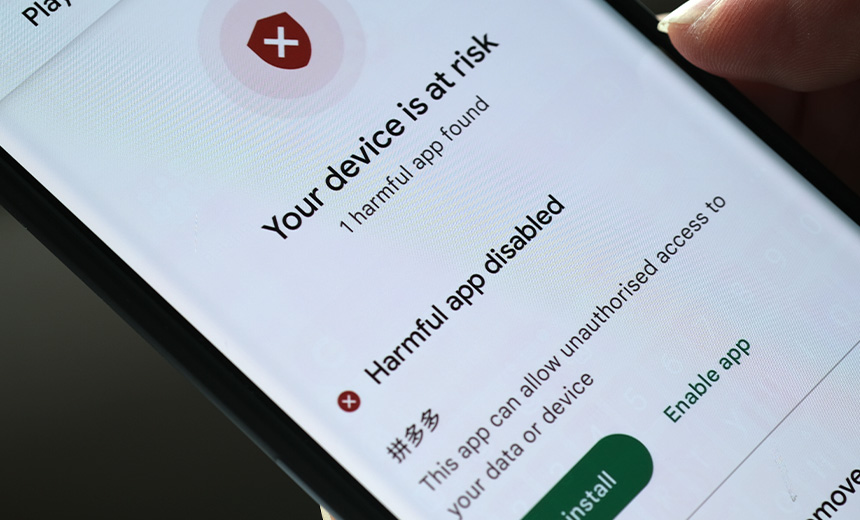
It is unclear whether the two malware types were distributed via Google Play Store or as .apk files. Lookout could not determine possible targets of APT41, as the campaign was not active at the time of analysis. Google said that “based on current detection, no apps containing this malware are found to be on Google Play.”
Though APT41 is not known for developing or distributing Android malware, the cybersecurity company said it came across several artifacts and forensic evidence during its analysis that helped it attribute the malware campaign to the Chinese cyberespionage group.
The first was the group’s use of similar Android signing certificates for both malware variants, but this isn’t sufficient for accurate attribution, as Chinese threat groups are known to share hacking tools and techniques. What clinched it for Lookout was that the malware’s command-and-control infrastructure featured the same IP address and web domain that APT41 had used in multiple campaigns between May 2014 and August 2020.
Lookout also found that the domain associated with WyrmSpy’s C2 infrastructure listed Jiang Lizhi as the registrant. In 2019 and 2020, a federal grand jury in Washington, D.C., indicted Lizhi, along with four other APT41 operators, for targeting over 100 organizations worldwide, including computer hardware manufacturers, telecommunications providers, universities, think tanks and foreign governments.
The five APT41 operators are still featured on FBI’s list of most wanted international fugitives.
Trend Micro in 2021 said APT41 also carried out a cyberespionage campaign in the Indo-Pacific region to target companies in India, Indonesia, Malaysia, the Philippines, Taiwan and Vietnam (see: APT41 Cyberespionage Campaign Hits Indo-Pacific).
Spyware Relied on System Permissions to Exfiltrate Data
Once inside an Android mobile device, both WyrmSpy and DragonEgg request extensive device permissions to perform surveillance. “WyrmSpy uses established rooting tools to gain escalated privileges to the device and perform surveillance activities specified by commands received from its C2 servers,” Lookout said. “These commands include instructing the malware to upload log files, photos stored on the device, and acquire device location using the Baidu Location library.”
The spyware contains the necessary functionality to exfiltrate log files, photos, device location, SMS messages and audio recording to the C2 server and if necessary, relies on a secondary payload to perform additional surveillance. DragonEgg also relies on a secondary payload named smallmload.jar that enables additional functionality and lets the malware exfiltrate device storage files, photos, contacts, messages and audio recordings.
“The discovery of WyrmSpy and DragonEgg is a reminder of the growing threat posed by advanced Android malware,” said Kristina Balaam, Lookout’s senior threat researcher. “These spyware packages are highly sophisticated and can be used to collect a wide range of data from infected devices.”
[ad_2]
Source link