[ad_1]
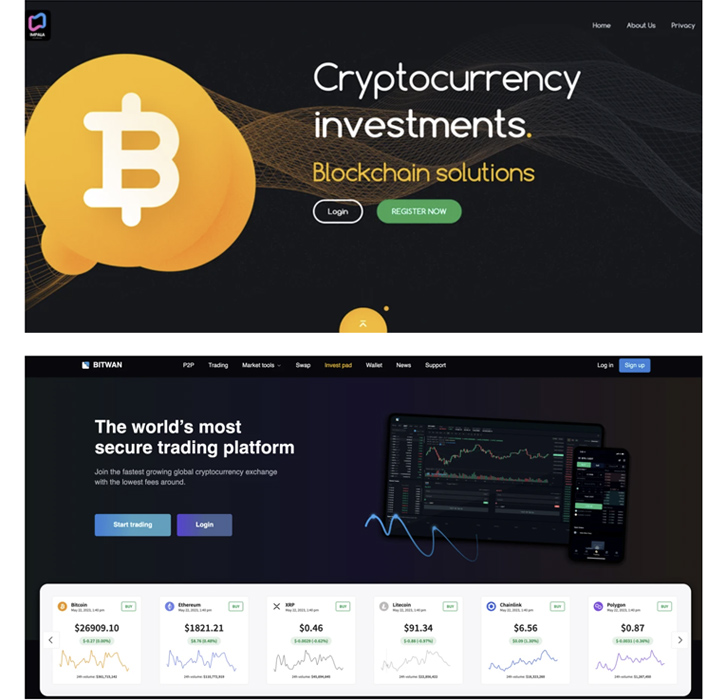
A previously undetected cryptocurrency scam has leveraged a constellation of over 1,000 fraudulent websites to ensnare users into a bogus rewards scheme since at least January 2021.
“This massive campaign has likely resulted in thousands of people being scammed worldwide,” Trend Micro researchers said in a report published last week, linking it to a Russian-speaking threat actor named “Impulse Team.”
“The scam works via an advanced fee fraud that involves tricking victims into believing that they’ve won a certain amount of cryptocurrency. However, to get their rewards, the victims would need to pay a small amount to open an account on their website.”
The compromise chain starts with a direct message propagated via Twitter to lure potential targets into visiting the decoy site. The account responsible for sending the messages has since been closed.
The message urges recipients to sign up for an account on the website and apply a promo code specified in the message to win a cryptocurrency reward amounting to 0.78632 bitcoin (about $20,300).
But once an account is set up on the fake platform, users are requested to activate the account by making a minimal deposit worth 0.01 bitcoin (about $258) to confirm their identity and complete the withdrawal.
“While relatively sizable, the amount necessary to activate the account pales in comparison to what users would get in return,” the researchers noted. “However, as expected, recipients never get anything in return when they pay the activation amount.”
A public Telegram channel that records every payment made by the victims shows that the illicit transactions have yielded the actors a little over $5 million between December 24, 2022, and March 8, 2023.
Trend Micro said it unearthed hundreds of domains related to this fraud, with some of them being active as far back as 2016. All the fake websites belong to an affiliate “scam crypto project” codenamed Impulse that’s been advertised on Russian cybercrime forums since February 2021.
Like ransomware-as-a-service (RaaS) operations, the venture requires affiliate actors to pay a fee to join the program and share a percentage of the earnings with the original authors.
To lend the operation a veneer of legitimacy, the threat actors are believed to have create a lookalike version of a known anti-scam tool known as ScamDoc, which assigns a trust score for different websites, in a plausible attempt to pass off the sketchy crypto services as trustworthy.
Trend Micro said it also stumbled upon private messages, online videos, and ads on other social networks such as TikTok and Mastodon, indicating that the affiliates are using a wide range of methods to advertise the fraudulent activity.
“The threat actor streamlines operations for its affiliates by providing hosting and infrastructure so they can run these scam websites on their own,” the researchers said. “Affiliates are then able to concentrate on other aspects of the operation, such as running their own advertising campaigns.”
🔐 Mastering API Security: Understanding Your True Attack Surface
Discover the untapped vulnerabilities in your API ecosystem and take proactive steps towards ironclad security. Join our insightful webinar!
News of the fake giveaway scam coincides with a fresh wave of cryptocurrency stealing attacks orchestrated by a threat actor dubbed Pink Drainer that has been found to masquerade as journalists to seize control of victims’ Discord and Twitter accounts and promote spurious crypto schemes.
According to statistics gathered by ScamSniffer, Pink Drainer has successfully compromised 2,307 accounts as of June 11, 2023, to steal more than $3.29 million worth of digital assets.
The findings also come weeks after Akamai took the wraps off a renewed Romanian cryptojacking campaign named Diicot (previously Mexals) that employs a Golang-based Secure Shell (SSH) worm module and a new LAN spreader for propagation.
Then last month, Elastic Security Labs detailed the use of an open-source rootkit called r77 to deploy the XMRig cryptocurrency miner in several Asian countries.
“r77’s primary purpose is to hide the presence of other software on a system by hooking important Windows APIs, making it an ideal tool for cybercriminals looking to carry out stealthy attacks,” the researchers said.
“By leveraging the r77 rootkit, the authors of the malicious crypto miner were able to evade detection and continue their campaign undetected.”
It’s worth pointing out that the r77 rootkit is also incorporated in SeroXen, a nascent variant of the Quasar remote administration tool that’s being sold for only $30 for a monthly license or $60 for a lifetime bundle.
[ad_2]
Source link