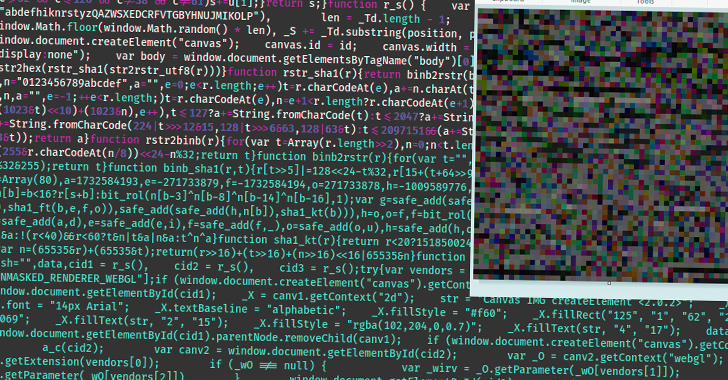
WoofLocker Toolkit Hides Malicious Codes in Images to Run Tech Support Scams
[ad_1] Aug 19, 2023THNMalvertising / Website Security Cybersecurity researchers have detailed an updated version of…
0 Comments